What is UConn’s Secured Research Infrastructure (SRI)?
Federal Government and Department of Defense related research contracts such as the DFARS 252.204-7012 clause and Export Control (ITAR/EAR), have required compliance with the Cybersecurity Capability Maturity Model (CMMC) 2.0 that includes the NIST SP 800-171 security controls to safeguard Controlled Unclassified Information (CUI). CUI is data that requires protection through dissemination controls pursuant to and consistent with applicable law, regulations and government-wide policies but is not classified. CMMC applies to CUI shared by or through the federal government with a nonfederal entity. As a higher educational institution, UConn is a nonfederal entity. There are 130 technical and operational controls specified by the CMMC/NIST standard and ITS has made every effort to reduce the compliance efforts for the Principal Investigator (PI).
The Secured Research Infrastructure (SRI) was developed with the intent of meeting the security control requirements while also reducing the workload on the PI to the smallest amount practical while still ensuring compliance. This solution meets 3 key design principles: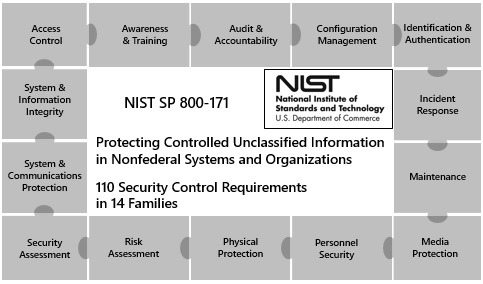
- The controls requirements established by the CMMC/NIST standard are complex. Completing the SRI Intake form, each research project will be reviewed for its specific technical requirements to properly safeguard CUI. Ensuring controls consistency reduces the time to bring a new project into the environment and increases the ability to ensure compliance.
- The system needs to provide the ability for researchers, whenever practical, to access and work with their data anywhere and have the environment be supported centrally.
- The security controls should be provided centrally. ITS made significant investments in our enterprise level security infrastructure and operational processes that enable us to protect CUI using centrally supported tools with more capabilities that can be provided locally.
Within the UConn Secured Research Infrastructure (SRI) Network, the PI and their researchers will access a virtual workstation remotely or through a dedicated SRI laptop or desktop with the ability to share data with those in the same research project. Remote access to the SRI allows connectivity to a secure network through network segmentation (provided by the VPN) and two-factor authentication (provided by DUO). While VPN/DUO accomplish the control requirements set by the CMMC/NIST standard, they provide the security needed to be able to access the SRI environment remotely.
Process of the Principal Investigator
The PI of the research project should have already met with a representative from OVPR’s Office of Sponsored Program Services and together determined that the research must comply with CMMC/NIST SP 800-171 standards. In addition, the PI should have already met with a representative from OVPR’s Export Control office and completed a Technology Control Plan (TCP).
During this process, the SRI Intake Form (see attachment below under Intake Form for PI) should be filled out and sent to the proper personnel to review the form and discuss any technical requirements for protecting the data within the CMMC/NIST SP 800-171 standards.
CMMC/NIST SP 800-171 Compliance Documentation
All compliance documentation related the research project will be stored in the System Security Plan (SSP). This SSP will enable any University audit or compliance staff to easily review how the 130 security controls are being established and maintained. CMMC/NIST also requires periodic risk assessments, which will be conducted periodically. Centralizing all infrastructure and technical documentation into a SSP will greatly reduce the work related to risk assessments while showing our due diligence is met regarding the security of the environment.
The PI is to ensure proper procedures of safeguarding CUI is maintained at all times with their entire research team. A PI should inform their system administrator and the CISO or designated ITS-ISO representative of any changes to their system. For example, installing new applications, new system requirements, and adding or removing access for research participants authorized in the TCP/TCSP.
Roles and Responsibilities
Four roles were identified as the OVPR and the ITS-ISO worked through determining responsibility for compliance. Individuals assigned to these roles will be documented in the SSP.
- Information System Owner/Principal Investigator
- ITS Common Control Provider
- System Administrator
- Chief Information Security Officer/designated ITS-ISO representative
The Information System Owner/Principal Investigator, herein known as PI, is a University official responsible for the procurement, development, integration, modification, operation, maintenance, and disposal of an information system. The information system owner is, most likely, the faculty member with primary responsibility for ensuring the project is completed. However, there may be key staff appointed by the PI that have responsibilities as well. PIs must adhere to the SRI PI Security Control Requirements & Checklist Summary.
The ITS Common Control Provider is an individual, group, or organization responsible for the development, implementation, assessment, and monitoring of common controls. Specifically this is any area within ITS that maintains a component of the secured research infrastructure. This may include the security office, server support, desktop support, etc.
The System Administrator is an individual responsible for ensuring that the appropriate operational security posture is maintained for an information system and as such, works in close collaboration with the information system owner. Typically the System Administrator works for the School or College the PI and their team is a part of. This individual is identified when the compliance initiative begins and will be documented as part of the SSP.
The Chief Information Security Officer is an organizational official responsible for carrying out the chief information officer security responsibilities under FISMA and serves as the primary liaison for the Chief Information Officer to the organization’s authorizing officials, information system owners, common control providers, and information system security officers.
NIST SP 800-171 Training Video
The UConn NIST SP 800-171 and security awareness training video provides a better understanding of the security controls required to meet the DFARS clause requirements.
Those identified whose research contract is under the DFARS clause who are involved with CUI or potential CUI data, an e-mail will be sent to take the NIST 800-171 and security awareness training. This 30 minute online video course is required and must be completed for CMMC/NIST compliance. Please login with your UConn NetID username and password to complete the training: 2020 NIST 800-171 and Security Awareness Training. Once logged in, click on Launch next to the course title to enroll and begin the training. This must be completed as noted or within 30 days of the research contract award date. Only those authorized to be in the SRI will receive the e-mail to take the training video.
Intake Form for PI
For an upcoming research project that will or may contain CUI as part of the DFARS clause or Export Control (ITAR/EAR), the PI should use the Intake Form to begin the process as they work on or complete their TCP/TCSP with the OVPR and before the contract has been awarded or upon award notification.
SRI Intake and TCP/TCSP Forms are available in KualiBuild.
SRI IT Support
All DFARS clause and Export Control research projects that contain or may contain CUI will have a designated technical representative or local system administrator to assist in the technical process.
Currently designated SRI and CMMC/NIST SP 800-171 trained technical support include:
| Laurie Neal Interim SRI Coordinator Information Security Office laurie.neal@uconn.edu |
Peter Menard ETS Director School of Engineering Phone: 860-486-5305 pete@uconn.edu |
Eric Soares IT Director, Supports CLAS College of Liberal Arts & Sciences Phone: 860-486-0478 eric.soares@uconn.edu |
| Robert Dowden Systems Administrator, Supports CLAS College of Liberal Arts & Sciences Phone: 860-486-5040 robert.dowden@uconn.edu |