What is a Phishing Attack?
A phishing attack is a scam and an effort to steal your personal information. Phishing attacks typically come in the form of fraudulent email messages that appear to have come from a legitimate source, such as your university or bank. Phishing emails will usually direct to a spoofed website or trick the receiver into divulging personal information like account passwords, credit card information, etc.
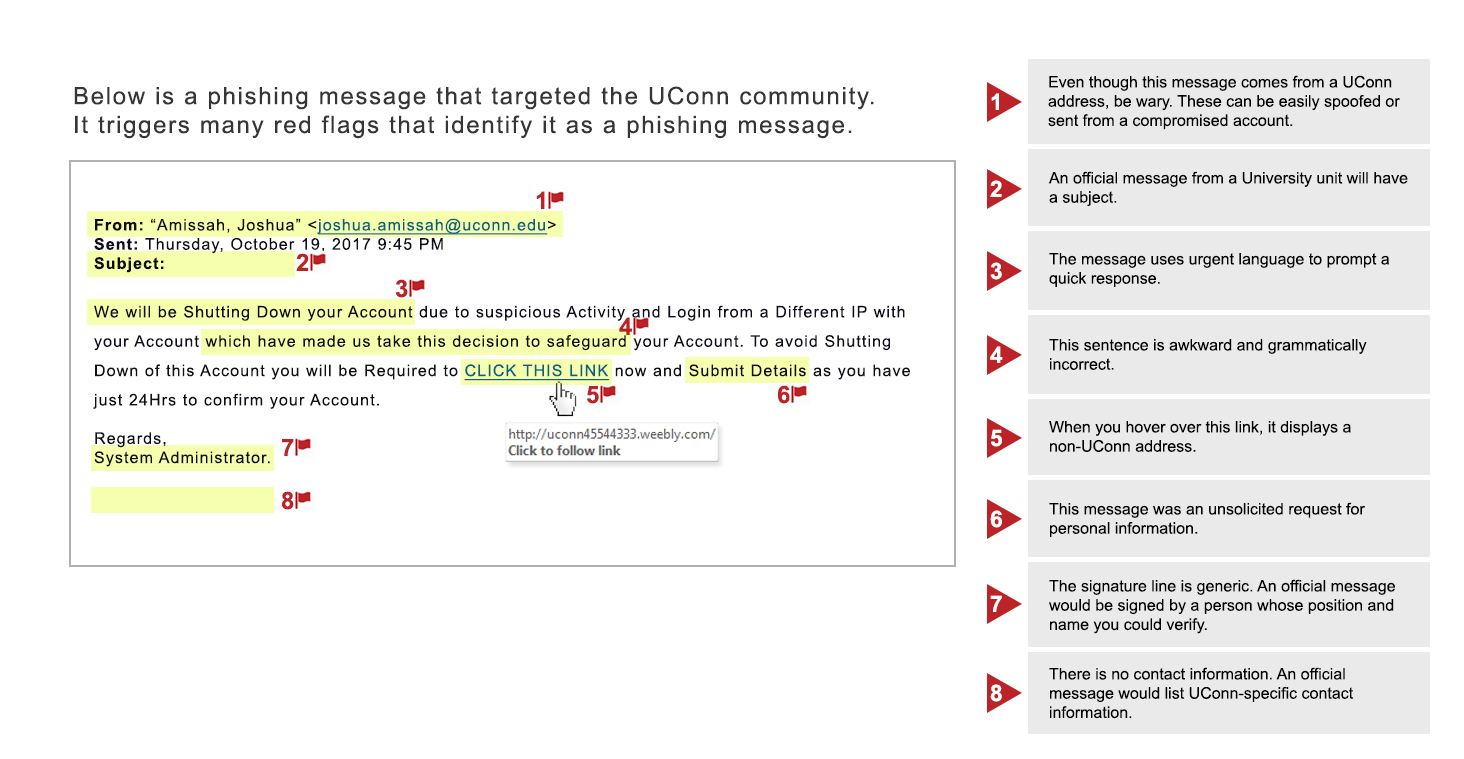
These attacks are often designed to appear urgent and panic recipients so that they take immediate action before verifying the legitimacy of the claim made. For example, a phishing email may claim the receiver will lose their account if they do not reset their password immediately through a provided link. Such claims are always indicative of a phishing scam as responsible companies and organizations would never take these actions via email.
If you receive a phishing email, it does not mean your account was hacked or a university system was compromised. Email addresses are publically available across many different websites and services, including the University Phonebook. All a phisher needs is your email address, and they can easily send you a fraudulent and misleading email. Education and awareness are the keys to protecting yourself and your private information.
How to Detect and Handle Phishing Messages
Step 1: Identify the message as a phishing scam.
Some red flags include:
- Urgent requests. Phishing attacks attempt to induce panic in the receiver and cause the person to act before investigating the authenticity of the request.
- Bad spelling or grammar. Phishing messages are notorious for containing misspelled words or poor grammar.
- Mismatched email address information. Make sure the email address displayed in the From: field matches address listed in behind mailto:.
- Generic signature line. A university message is typically signed by a university official, whose name you can verify, and have credible contact information.
- Unexpected requests regarding personal information. Be extremely wary of following links or answering questions from contacts you did not initiate.
Step 2: Check out links and attachments before you click.
- Links can direct you to spoofed web pages or download harmful files on your system. You can hover the cursor over the link before you click on it to ensure that the address matches the link that was typed. You can always check the legitimacy of a message by going directly to the company or organization website or contacting them via phone.
- Hover over an attachment to verify that the title matches the file type. A document that looks like it has a name “something.pdf” might actually be a file “something.exe.” An .exe extension means the attachment is actually a software program that you execute and is extremely dangerous; it can cause computer infection and data loss.
Step 3: Report and delete
If you suspect that the email is a phishing message, please report it by using the Report Phishing button within Outlook.
Security Service Update
UConn has enabled Advance Threat Protection (ATP) on all University email services. ATP provides protection against malicious links and unsafe attachments.
- Links: All URLs are rewritten through Office 365. If a link is safe, you will still go to the intended location. If a link is unsafe, you will see a warning message.
- Attachments: All attachments are scanned for malware and access to attachments considered unsafe will be blocked.
Before implementing this service, ITS would advise you to hover over links and attachments and ensure that the link and address matched. With this service, all links are rewritten in Office 365 and will not match the URL displayed in the message.
ATP provides you with additional protection from unsafe links and attachments. However, continue to exercise caution and do not click on suspicious links. No detection method can provide complete protection.
How to Report a Phishing Attack
When you recognize a phishing attack, you should report it to ITS to help protect yourself and others. To submit a phishing message, please use the Report Phishing button in Outlook. For detailed instructions on where the button is located and how to use it, you can visit this article, Reporting Spam and Phishing Messages - Information Technology - UConn Knowledge Base.
What to do if you clicked on the link
If you have clicked on a link in a phishing email or given personal account logins or information be sure to take the following steps immediately.
- Change your password directly through the company or organization's official website. For extra certainty, type the address into your web browser directly. For the UConn community you can change your NetID password at netid.uconn.edu.
- Review account statements and activity. It should also be noted that ITS monitors for suspicious activities associated with phishing attacks.
- Run a virus scan on your computer to detect and remove any potentially harmful software downloaded on your system after clicking on a link.
If you have questions about the validity of a request, contact the ITS Technology Support Center at 860-486-4357 or techsupport@uconn.edu.